macOS - HighSierra Root Without A Password & How To Fix!
Email: yieldtekco@gmail.com
YouTube: youtube.com/channel/UCD5ncv9WJL54GHfxjNpeNNA
Live Stream: twitch.tv/hightekgrow
Github: github.com/YieldTek
Discord: discord.gg/xgmGyE6
Website: yieldtek.com
Facebook: facebook.com/hightekgrow
Twitter: twitter.com/HighTekGrow
Reddit: reddit.com/r/hightek/
Support HighTek: patreon.com/hightek
Donations: paypal.me/atarimaster
Today it was shared with the world that there is a massive bug in the latest updates to the macOS. HighSierra seems to have a bug that only effects system that got HighSieera through an update. This means if your machine came pre-installed with HighSierra you are not effected by this bug. This bug allows the users to bypass authentication when accessing anything that requires privilege escalation. This is anything from changing settings to installing certain apps.
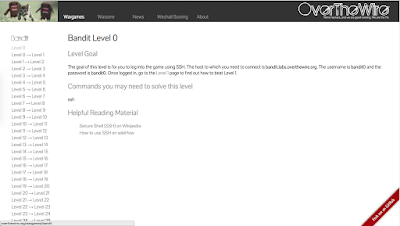
You can test this out yourself and see if your machine is affected first hand by opening up your System Preferences and going to the Users & Groups tab shown below.
Once you are in the users and group tab click the lock icon on the bottom left-hand side of the screen as shown below.
This will open up an authentication prompt asking for your username and password. Replace your username with the username 'root' and click unlock. It will fail the first time but if you click it a few more times quickly(spam click it) it will unlock and the lock icon will change to the one shown below meaning you are authenticated and able to change settings.
YouTube: youtube.com/channel/UCD5ncv9WJL54GHfxjNpeNNA
Live Stream: twitch.tv/hightekgrow
Github: github.com/YieldTek
Discord: discord.gg/xgmGyE6
Website: yieldtek.com
Facebook: facebook.com/hightekgrow
Twitter: twitter.com/HighTekGrow
Reddit: reddit.com/r/hightek/
Support HighTek: patreon.com/hightek
Donations: paypal.me/atarimaster
[ What and Who ]
Today it was shared with the world that there is a massive bug in the latest updates to the macOS. HighSierra seems to have a bug that only effects system that got HighSieera through an update. This means if your machine came pre-installed with HighSierra you are not effected by this bug. This bug allows the users to bypass authentication when accessing anything that requires privilege escalation. This is anything from changing settings to installing certain apps.
[ How To Test ]
You can test this out yourself and see if your machine is affected first hand by opening up your System Preferences and going to the Users & Groups tab shown below.
Once you are in the users and group tab click the lock icon on the bottom left-hand side of the screen as shown below.
This will open up an authentication prompt asking for your username and password. Replace your username with the username 'root' and click unlock. It will fail the first time but if you click it a few more times quickly(spam click it) it will unlock and the lock icon will change to the one shown below meaning you are authenticated and able to change settings.
[ Wrap Up ]
For now, there isn't much we can do other than sit back, crack open a beer an wait for Apple to release a patch. Let me know what you think on this whole thing and if you feel that it isn't okay for Apple to release software with bugs like this. Happy hacking and don't forget to give this post the +1 and keep coming back for more content like this!






Comments
Post a Comment